Trezor Login – Your Ultimate Gateway to Crypto Security
Master the art of secure cryptocurrency access with Trezor Login. Learn how this cutting-edge authentication method protects your assets with hardware-level encryption and zero-trust architecture.
🔍 What is Trezor Login?
The Trezor Login system is your key to accessing digital assets without ever exposing your private keys online. It’s a physical verification process integrated within Trezor Suite, designed to keep crypto users safe from phishing, malware, and remote attacks.
Unlike browser-based logins, Trezor Login requires device confirmation for every transaction, ensuring that only the rightful owner can approve operations. This offline-first approach makes it one of the most trusted systems in the crypto world.
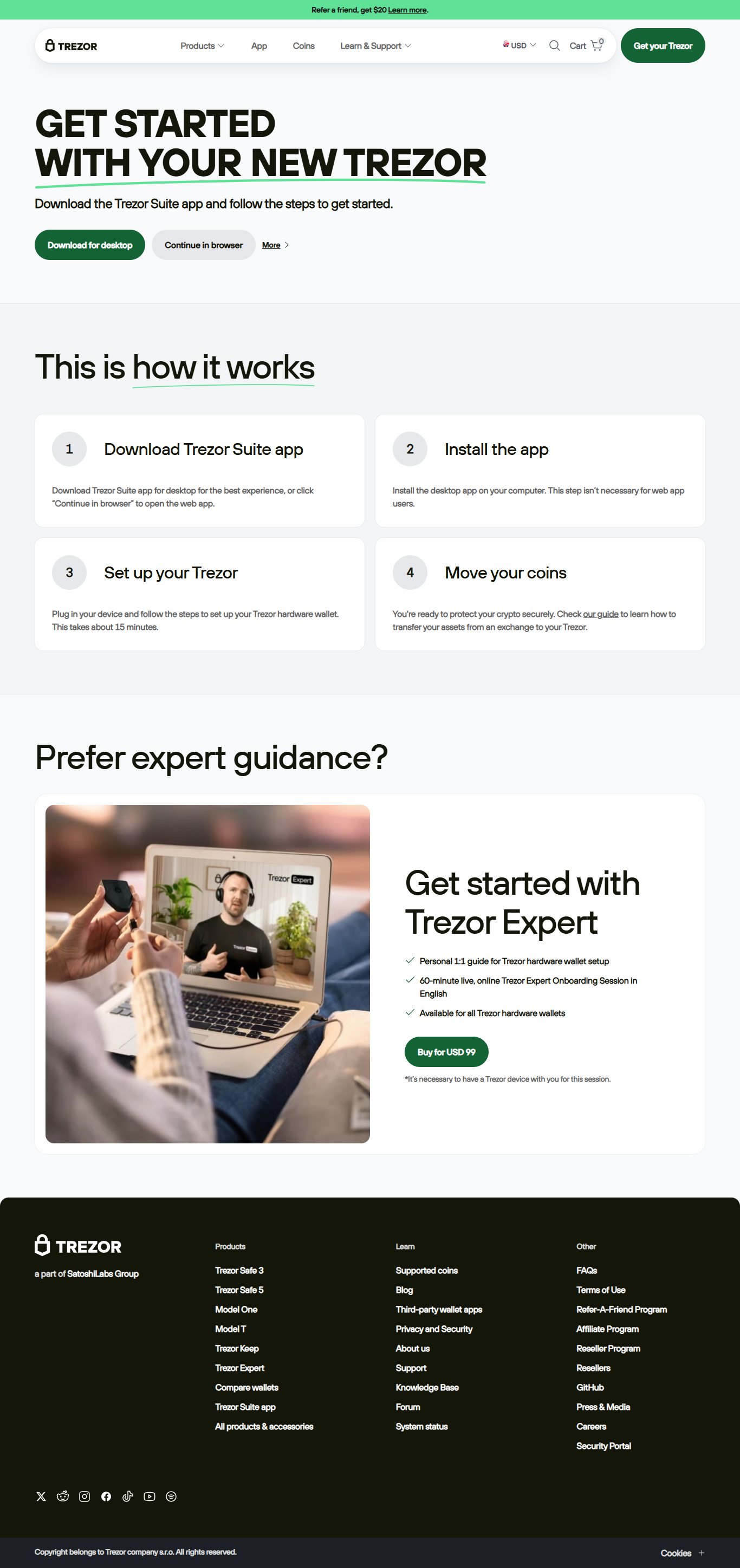
🧭 Step-by-Step Process of Trezor Login
Step 1: Connect Device
Connect your Trezor Model T or Trezor One to your computer or mobile using the original cable.
Step 2: Open Trezor Suite
Launch the Trezor Suite application. This secure platform allows you to manage, exchange, and view your crypto portfolio.
Step 3: Verify Device Authenticity
The app automatically verifies the firmware and authenticity of your hardware wallet to block counterfeit access.
Step 4: Enter Your PIN
Input your PIN using the randomized grid displayed on the device screen, preventing keylogging attacks.
Step 5: Access Your Wallet
Once verified, your dashboard unlocks, giving you full control over sending, receiving, and tracking crypto assets.
🧱 Why Trezor Login is the Safest Choice
- Offline Key Storage: Private keys never leave your hardware device.
- Physical Confirmation: Every transaction must be verified manually on your device screen.
- Transparent Open Source: Fully auditable code ensures trust and accountability.
- Multi-Asset Compatibility: Works with Bitcoin, Ethereum, and 1000+ supported tokens.
- Recovery System: Restore access anytime using your recovery phrase.
💡 Pro Tips for a Secure Login
✅ Check the URL
Always use Trezor.io or the official Trezor Suite app. Avoid lookalike domains and fake pop-ups.
✅ Keep Firmware Updated
Updates often contain essential security patches and improvements to keep your device safe.
✅ Secure Your Recovery Phrase
Store your seed phrase offline and never share it digitally. It’s your ultimate backup key.
✅ Avoid Third-Party Apps
Only log in via the official Trezor Suite or verified browser extensions.
⚠️ Troubleshooting Common Login Errors
| Problem | Possible Cause | Solution |
|---|---|---|
| Device Not Detected | Faulty cable or outdated driver | Reconnect using original cable and update Trezor Bridge drivers. |
| PIN Entry Fails | Incorrect grid mapping | Retry—remember grid positions change every login. |
| Suite Not Opening | Corrupted installation | Reinstall the app from the official Trezor.io website. |
🧠 Inside Trezor Suite: Managing Assets Post-Login
Once logged in, Trezor Suite becomes your all-in-one control center. You can track balances, make transactions, and integrate with DApps — all secured by hardware-level authentication.
Through Trezor Suite, users can access DeFi platforms, stake assets, and monitor portfolio growth in real time, with every operation double-confirmed via the Trezor device screen.
📚 Frequently Asked Questions
Q1: Is Trezor Login free?
A: Yes, Trezor Login is completely free with your Trezor device and official Suite app.
Q2: Can I log in from multiple computers?
A: Absolutely. As long as you use your Trezor device and PIN, you can log in from any trusted computer.
Q3: What if I lose my Trezor device?
A: Use your recovery phrase to restore all assets on a new device.
Q4: Is it possible to use Trezor Login for Web3 apps?
A: Yes, Trezor integrates with multiple DApps for secure decentralized access.
Trezor Login – Confidence Meets Convenience
The Trezor Login process is not just an entry point—it’s your shield against digital theft. With every login, you assert full control, transparency, and ownership of your crypto future.
Trezor: Unlock Freedom, Securely.